

YuJa Himalayas Enterprise Archiving Platform provides tools for enterprises to manage large data workloads in a secure, compliant, and discoverable manner.
YuJa Himalayas is built in the cloud to efficiently manage large data workloads, identify compliance issues, and enable e-discovery scenarios.
Archive and manage your digital media securely
Integrates with video CMS, video conferencing and LMS tools
Real-time data ingestion and archiving
Create a central backup strategy with cloud and offsite endpoints
Real-time notifications and comprehensive audit logs
Comprehensive reporting and configurable analytics
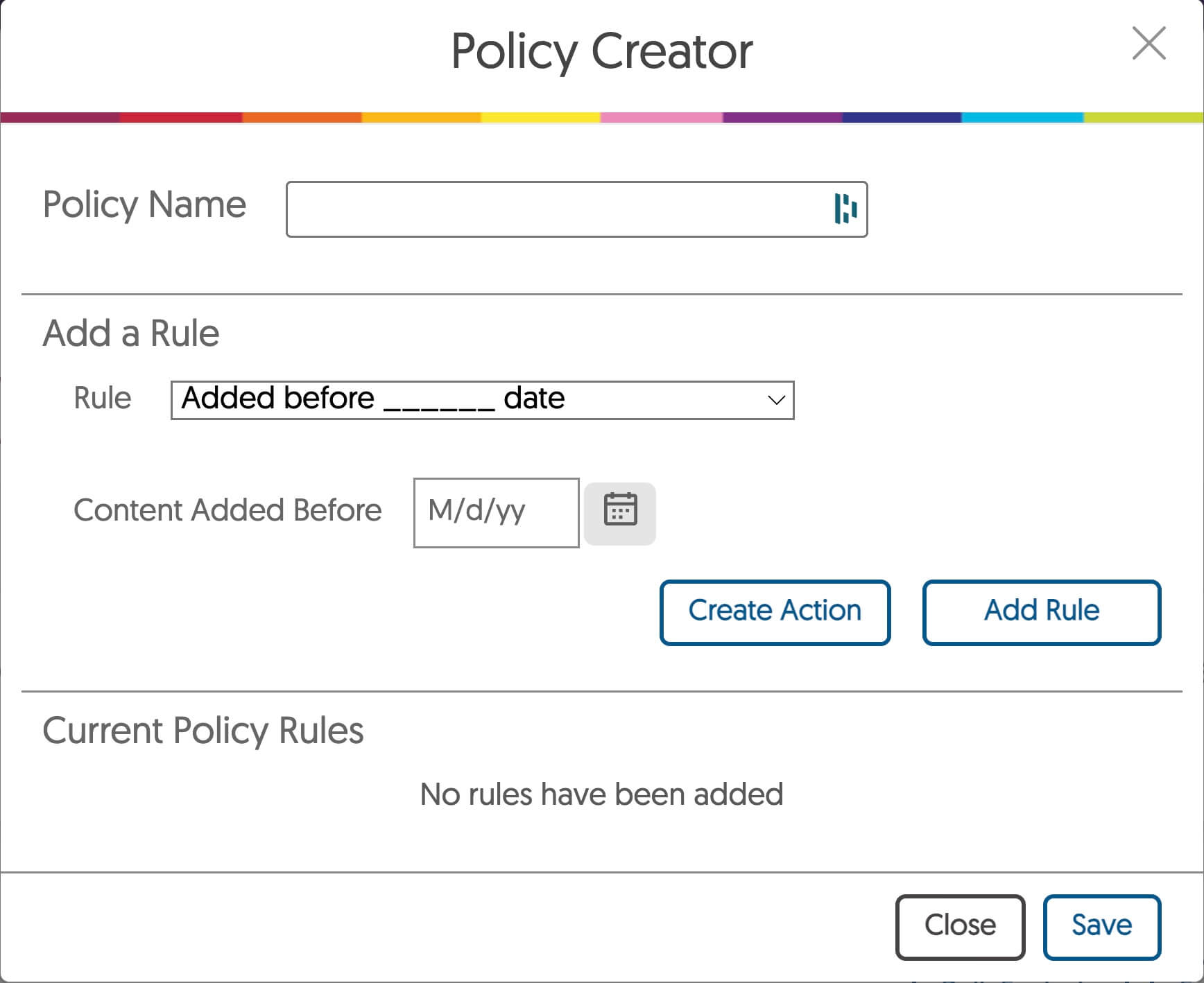
Customizable data policies and rulesets
Ability to create automated and recurring data policies
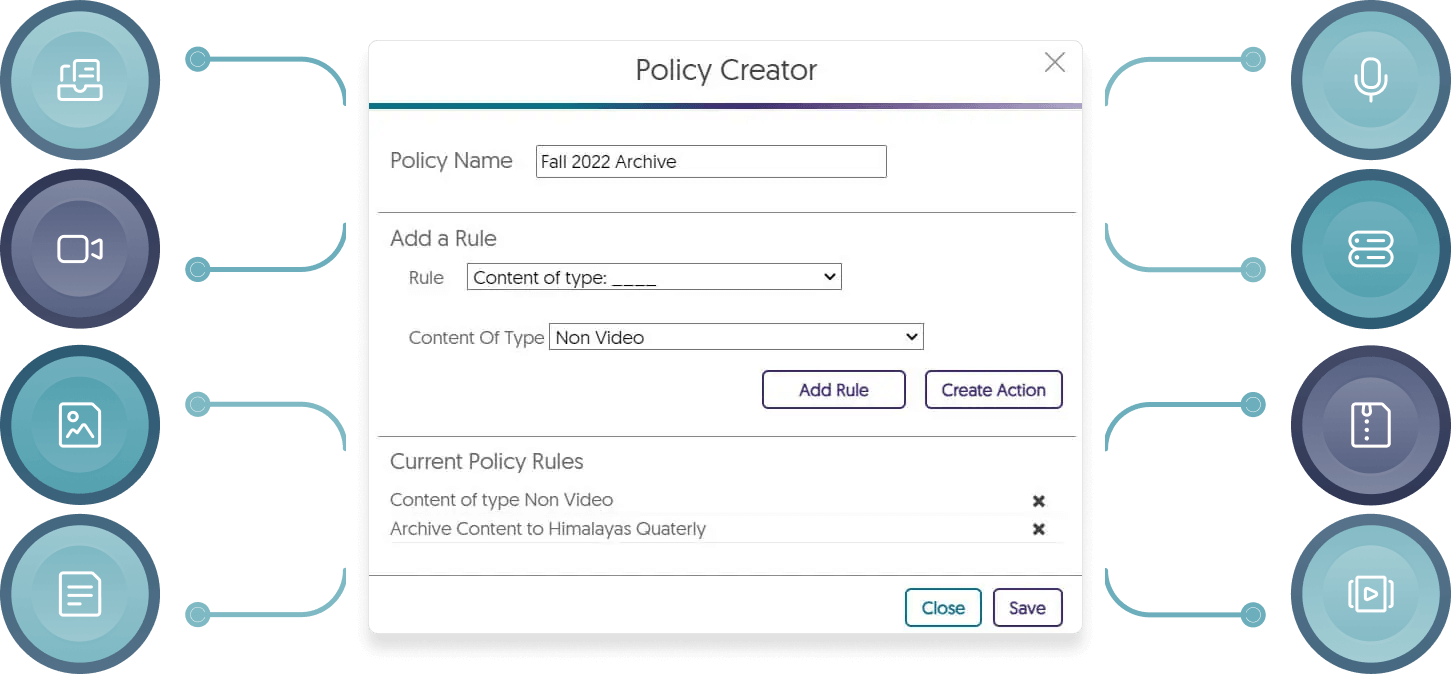
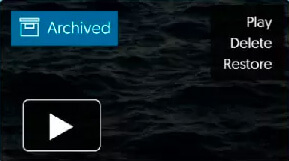
YuJa Himalayas offers the ability to define customized data policies that can automatically govern how content is archived, retrieved, purged or segmented.

As the committee searched for the right product, Leo said there was an immediate attraction to YuJa. “The Video Platform was so compelling, not only compared to what we were coming from, but also what was available in the marketplace,” he stated. “It was night and day, competitively speaking.”
Read the case study
YuJa Himalayas provides automated ingestion from video conferences including chats, polls, and transcripts. This enables detection of audio and video content, workflows to help reviewers identify media content for deeper analysis, and the ability to define data policies.
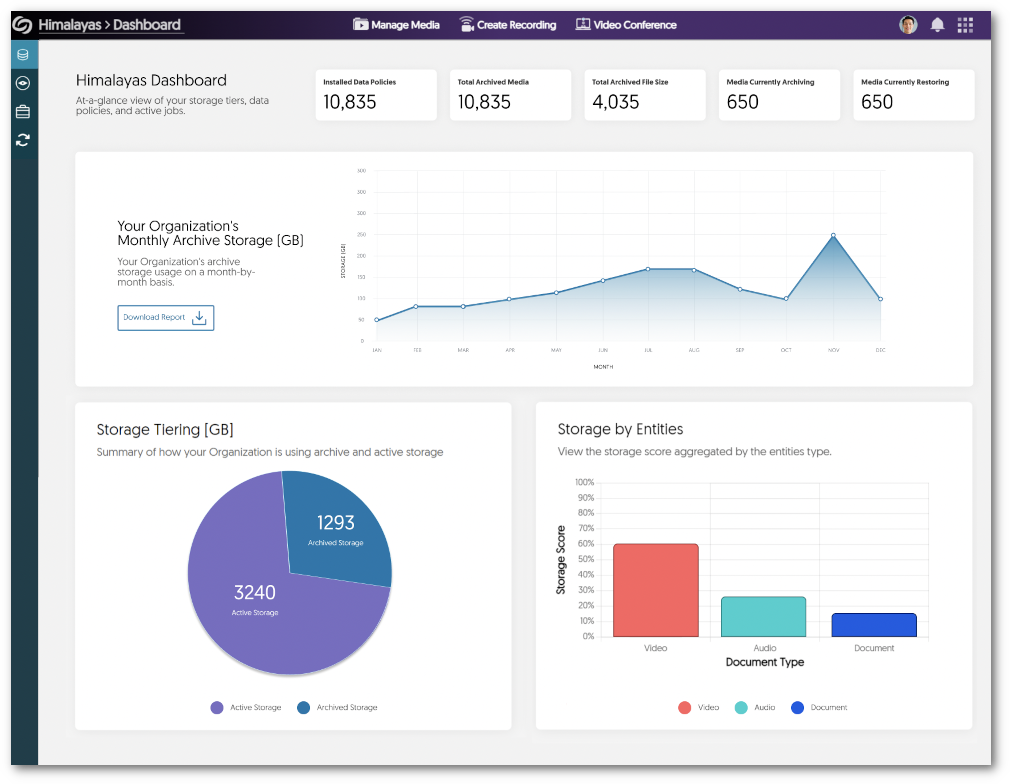
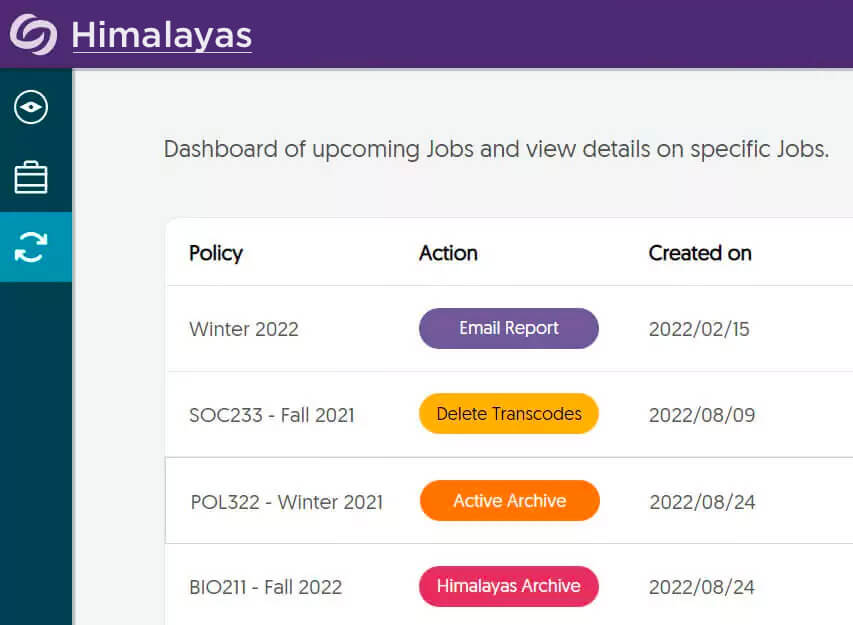
To facilitate the effective administration and review, Himalayas offers comprehensive analytics, reporting and dashboards. These reports offer graphs to view monthly storage use, a breakdown of files stored within Active Storage and Archived Storage, and the types of formats stored on the platform.

As organizations scale video and audio collaboration, the challenge of compliance makes it difficult to increase usage within regulated sectors. YuJa Himalayas provide a unified Platform to review and search video conference recordings, analyze and search visual content, and provide compliant archiving of video content.
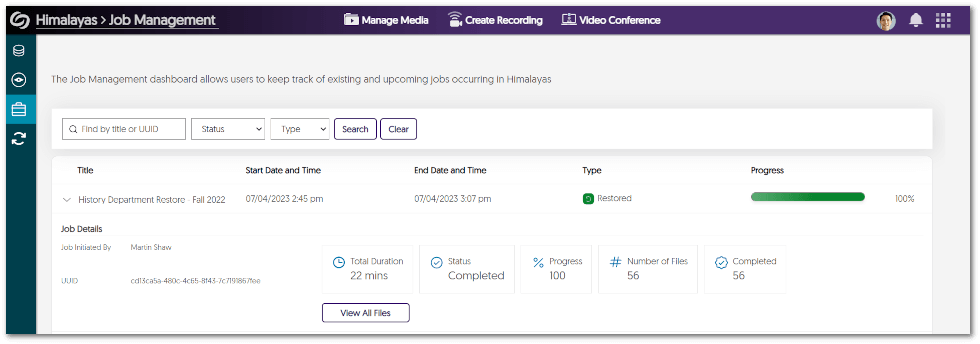
To provide administrators with comprehensive insights into their active archiving requests, we provide detailed information for each individual Job. Administrators can effortlessly access data that includes the number of files archived/restored, the number of completed/failed files, and the number of pending files.

Himalayas automatically provides tools to identify regulatory and corporate compliance risks in video, audio, and documents by providing the searchable transcriptions of spoken words, and optical character recognition (OCR) of screen content.

YuJa Inc. is a SOC 2-compliant firm achieving the highest standard for corporate and information technology (IT) governance. YuJa contracts with an experienced compliance auditing firm that holds designations as a Certified Public Accountant (“CPA”), Certified Information Systems Auditor (“CISA”), Certified Information Systems Manager (“CISM”), and Certified Internal Auditor (“CIA”). These audits are performed annually with quarterly checkpoints to perform testing of the compliance controls that are in place.